Sigma rule easeroden
Kaspersky actively involves SIGMA in its practice: the latest report on crimeware, " The common TTPs of modern ransomware groups ", includes over 70 SIGMA rules that simplify the work of security specialists. During this webinar, Kaspersky experts will provide a short overview of the SIGMA history, explain the main technical details - and.

Sigma Rule Attitude Whatsapp Status Video, Best Attitude HD Status Video
Luckily, Sigma rules (a use-case converted into the Sigma specification is called a rule) serve as a strict format for analysts to describe a particular use-case and convert it for whichever.
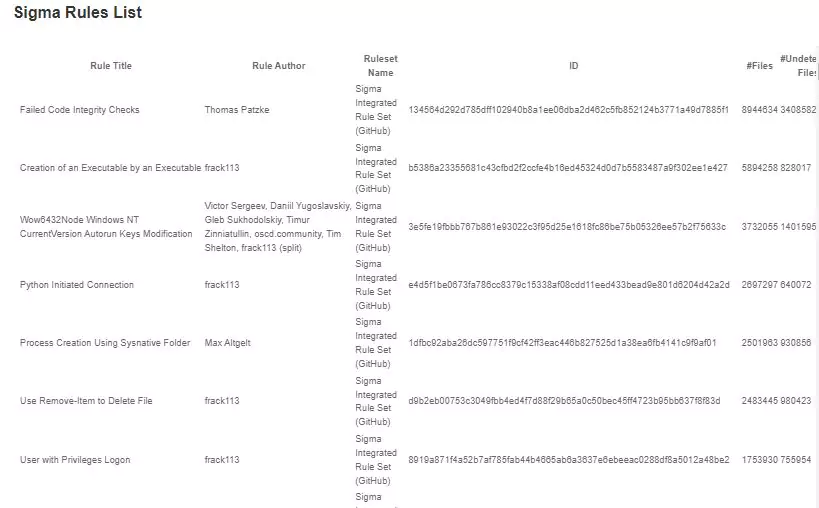
[PDF] Sigma Rules List PDF Panot Book
Threat Hunting Sigma rules can be used to hunt for threats: Use the rules to detect when a certain attack or threat targets your organization. Check if your organization was breached by applying Sigma rules to old logs (assuming your organization aggregates logs for at least a few months).

What the HELK? SIGMA integration via Elastalert by Roberto Rodriguez
Sigma rule for NotPetya Ransomware Activity detection was developed and shared with the community by Florian Roth and Tom Ueltschi. Simultaneously, the SOC Prime Team helped the victims of the NotPetya attack on-site and remotely using Sigma rules alongside its own SIEM-native content..

15 Signs You’re An Alpha Male
What Is Sigma Rule? A Sigma rule is an open-source, generic signature format used in cybersecurity, specifically for the creation and sharing of detection methods across Security Information and Event Management (SIEM) systems. Sigma rules translate and standardize threat-detection practices, making them accessible and reusable regardless of.
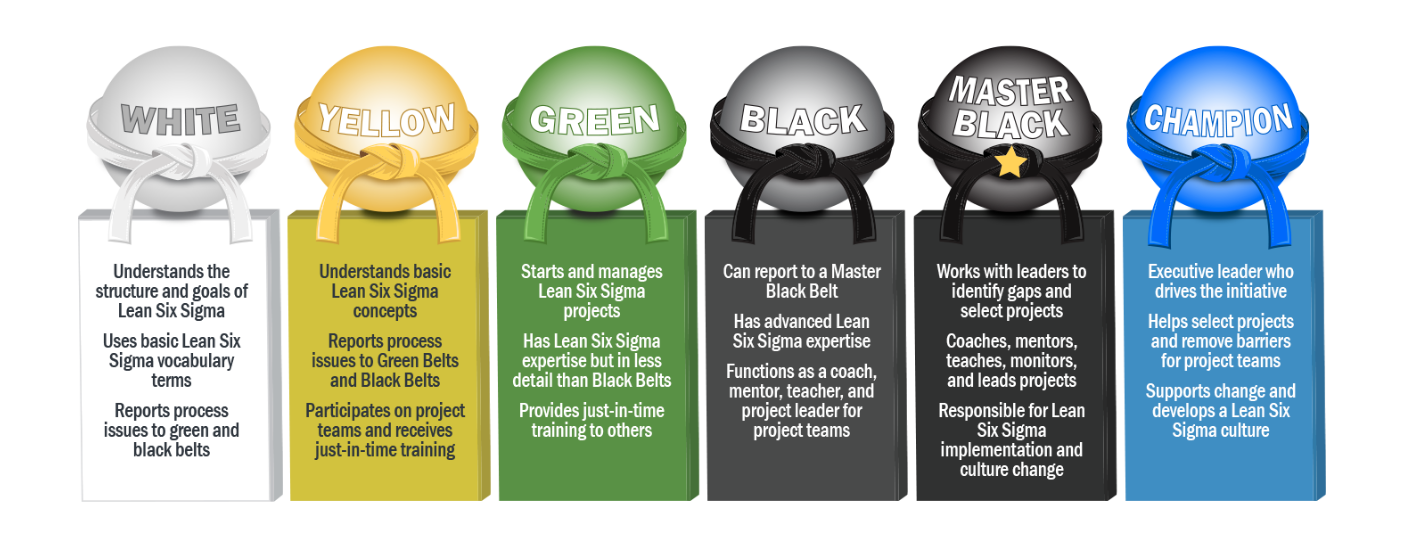
What Is Six Sigma?
What are Sigma Rules? Introduced in 2017 by detection engineer Florian Roth and open-source security tool developer Thomas Patzke, Sigma is a text-based, generic, open signature format that analysts can use to describe log events, making detections easier to write.
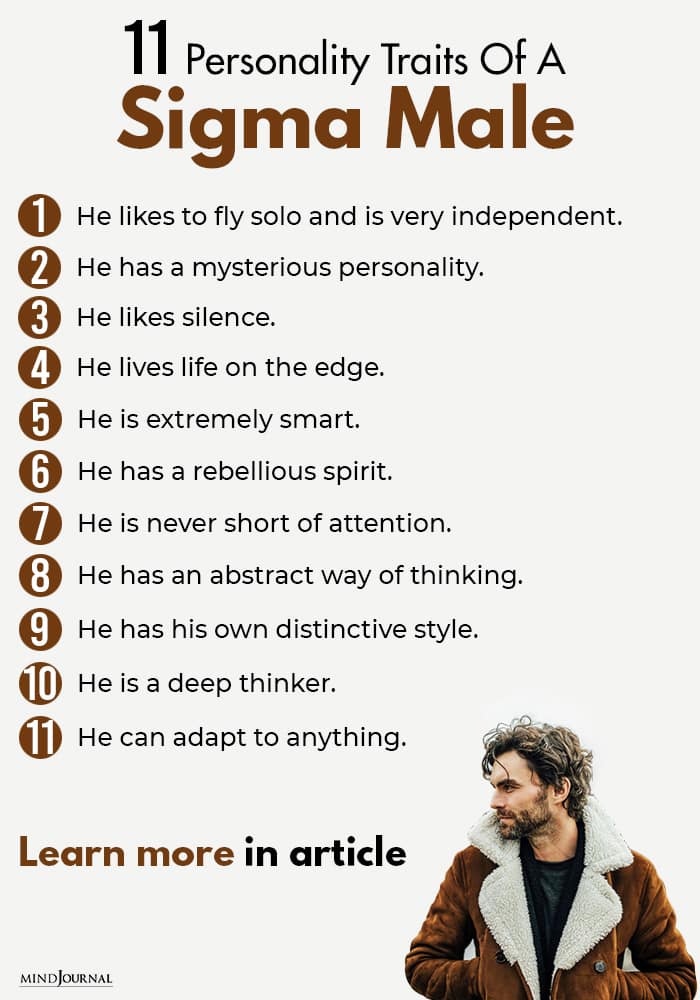
11 Personality Traits Of A Sigma Male That Sets Them Apart (2023)
Sigma rules are YAML files that contain all the information required to detect odd, bad or malicious behaviour when inspecting log files - usually within the context of a SIEM.

Alpha Male Characteristics, Alpha Male Traits, Male Mindset, Male Logo
SOC Prime users are now armed with high-quality detection content to proactively defend against the most common adversary behaviors and tools applied by threat actors in destructive cyber-attacks. The Sigma Rules list called "Smoking Guns" is based on the recommendation engine that harnesses collective industry expertise and peer-driven.

Sigma Rule Memes And Meme Sound Download Memes.co.in
May 16, 2022 · 14 min read The Case for SIGMA Rules Creating SIGMA Rules Recommended Background & Context Let's Create a Simple SIGMA Rule! An idea (and some thoughts on detection engineering with SIGMA) A data source / A log source Fitting the detection idea to SIGMA Logsource component Detection component Selection sub component (s):

60+ best sigma male quotes and captions for your photos Tuko.co.ke
The Smoking Guns Sigma Rules list serves as a universal solution for a wide cybersecurity audience offering high-fidelity alerts to identify critical security gaps and providing an immense.
Understand Sigma Male; Characteristics, Traits, And Rules
0x2 : General specifications of Sigma Rules. The sigma rule consists of the following sections, we will understand it with one of third party Sigma Rule, which has been downloaded from the.
The Lone Wolf Who Is He? The Sigma Male Personality Traits You Need To
Article Last Updated on Tue June 21, 2022 A deep dive into Sigma rules and how to write your own threat detection rules Written by Hardik Manocha Co-founder @ FourCore Sigma as a Detection Language In our previous blog post, we covered how Windows Event Log IDs can be utilized for threat hunting, featuring Sigma rules.
mexicoukraine Blog
Sigma rules are textual signatures written in YAML that make it possible to detect anomalies in your environment by monitoring log events that can be signs of suspicious activity and cyber.

Pin on Lifestyle
List of open source community Sigma rules that match the sysmon events recorded via execution of the file under scrutiny in a sandbox. Number of matching Sigma rules of all the different severities. Number of matching Sigma rules of this specific severity. Sigma rule name. Sigma rule description. View the Sigma rule.

8+ Sigma Omegaverse RohitEleanore
Sigma Rules Examples 0xffccdd · Follow 3 min read · Dec 2, 2022 Sigma rules are a powerful tool for enhancing the capabilities of SIEM (Security Information and Event Management) systems.

[PDF] Sigma Rules List PDF Download PDFfile
Sigma Rules List; Sigma rules; Crowdsourced YARA Rules; Get Started; Searching; Sigma Rules List Powered by Zendesk.